how to become cyber insurance ready

How to Apply for Cyber Insurance
The following are the key elements that insurance companies are looking for to qualify your business for cyber insurance coverage.
Your best resource is a Staebler Broker who can help you navigate cyber insurance.
They can make sense of what’s required from you and provide recommendations to help protect your business’ valuable assets.
Special thanks to our network solutions partner Fortify for their assistance and expertise with this information.
get your business cyber insurance ready

ACCESS CONTROL
- Password Policy – complexity and forced regular changes
- Multi-Factor Authentication – for multiple access points
- Remote Access – Work From Home security
- Password Management – software to securely store
- Zero Trust Network Access (ZTNA) Strategy
- Dark Web Research and Monitoring

PERIMETER
- Firewall – implemented and managed
- Web Content Filtering – browsing the Internet is filtered
- Intrusion Detection System (IDS) – detect attacks
PATCH & UPDATE
- Operating Systems – servers and workstations
- Applications – individual user software
- Devices – firmware and systems

DATA
- Databases – encrypted at rest
- Other Data and Files – encryption at rest
- Backups – frequency, transferred offsite, testing of restoration, data AND critical servers/workstations

MONITOR & SCANNING
- Network Monitoring – detects performance issues
- Vulnerability Scanning – perimeter, applications, devices
- Penetration Testing – test ability to break in to network
- Security Information & Event Management (SIEM)
- Security Operations Centre (SOC)

DOCUMENTATION & PROCESS
- Business Continuity & Disaster Recover Plan
- Email & Internet Usage Policy – including social media
- Incident Response Policy
- Security Policy – how is information secured and stored?
- Change Management/Control Procedure

- Filtering – scanning emails for threats and spam
- Advanced Threat Protection – sandboxing of attachments
- DNS Management – email authentication/validation such as SPF, DKIM, Sender ID, or DMARC
- Data Loss Prevention

PEOPLE & BEHAVIOUR
- Cybersecurity Awareness Training and Testing
- Physical Building Security Measures

DEVICE SECURITY
- Virus/Malware Protection – servers & workstations
- Endpoint Detection & Response – servers & workstations
- Mobile Device Management – secure and manage access
- Asset Management – track and cycle older devices
Get A Quote
Fill in the form and one of our brokers will contact you soon.
Cyber Insurance
Why Insure with Staebler?
Working with a broker brings experience, expertise, and advocacy to you and your organization. With an individual broker, you have the ability to personalize your insurance solutions for your unique needs. Find out why there are 7 Really Good Reasons to use an Insurance Broker.
Related Blog Posts
Do You Have Adequate Coverage Limits?
Do You Have Adequate Coverage Limits? In our previous post, we asked this question: True or False: Insurance brokers are provincially regulated. Answer: Yes, they are! Insurance brokers are regulated by the Registered Insurance Brokers of...
Ethical Terminating Practices
Ethical Terminating Practices In our previous post, we asked this question: Even businesses need Emergency Supplies. How many days’ worth of emergency supplies are recommended to be kept on hand for the average number of people on the premises? Answer: For a business...
Disaster Preparedness for Businesses
Disaster Preparedness for Businesses In our previous post, we asked this question: The airline Virgin America has an official customer service goal: They will respond to Tweets within ___ minutes. But often, they’re able to respond within ___. Answer: The airline...
Ten Ways to Attract New Customers Online: Part Three
Ten Ways to Attract New Customers Online: Part Three In our previous post, we asked this question: How many truck driving jobs were there in Canada in 2012? Answer: According to one analysis, in 2012 there were over 240,000 truck driving jobs in Canada—an increase of...
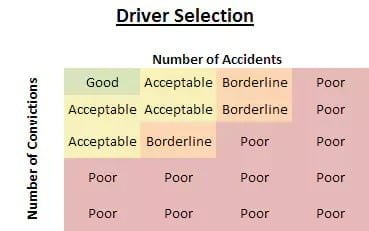
Tips on Hiring a Driver for Your Business
Tips on Hiring a Driver for Your Business In our previous post, we asked this question: True or False: Workplace violence is a term limited to incidents that occur within a traditional workplace. Answer: False. Workplace violence can also refer to incidents that...
Preventing Violence in the Workplace
Preventing Violence in the Workplace In our previous post, we asked this question: Studies show that drivers who use cell phones while driving are how many times more likely to get into a collision than a non-distracted driver? Answer: According to a study by the...
Ten Ways to Attract New Customers Online: Part Two
Ten Ways to Attract New Customers Online: Part Two In our previous post, we asked this question: How long do you have to grab & hold the attention of a potential customer visiting your website? Answer: You have 5-10 seconds to grab a visitor’s attention… but...
Ten Ways to Attract New Customers Online: Part One
Ten Ways to Attract New Customers Online: Part One In our previous post, we asked this question: What is the best temperature at which to use a block heater for your car? Answer: The best time to plug in your block heater is when the temperature dips below -15˚C. The...
Cyber Crime
Business Interruption Trivia Time In the previous post, we asked the question: According to recent statistics, approximately how many identity theft complaints per month do Canada?€?s largest credit bureaus receive? Answer: Statistical information from Equifax and...
Business Interruption
Business Interruption Trivia Time In the previous post, we asked the question: According to recent statistics, approximately how many identity theft complaints per month do Canada?€?s largest credit bureaus receive? Answer: Statistical information from Equifax and...
Small Companies are targets for Cybercrime
A recent study reported that small businesses are cybercriminals' favourite target for two reasons: they have a lot worth stealing such as bank account information, customer data, and intellectual property, and they often lack adequate security practices and...
Cost of Risk
I recently came across an article entitled "Risk Calculator". The article touched on some familiar concepts for Risk Managers; "Cost of Risk", but it certainly does apply to all business owners. If you go to the internet you will find many different perspectives on...